- Offers
- Product Philosophy
- Products
-
-
-
Traversals Government
- Ukraine Dynamic Frontline MonitoringAllows organizations to track frontline changes in almost real-time.
- Emerging Diseases RadarAllows organizations to identify new and emerging diseases in near real-time.
- Multi-Source Data Fusion PlatformAllows organizations to set up enterprise multi-source data and information fusion.
- Custom ServicesCustomized services can be provided at any time.
-
-
-
- Technology
- Company
-
-
-
Who We Are
- Our StoryMake Data Speak Your Language – Data fusion for comprehensive transparency, security and a secure basis for decision-making.
- CareersAre you interested in contributing to the development of exceptional solutions?
- ContactGet in contact with us if you need customized services or have questions.
-
-
-
Legal Information
- Legal Disclosure
- Privacy Policy
-
-
-
- Blog
- Contact Us
- Login
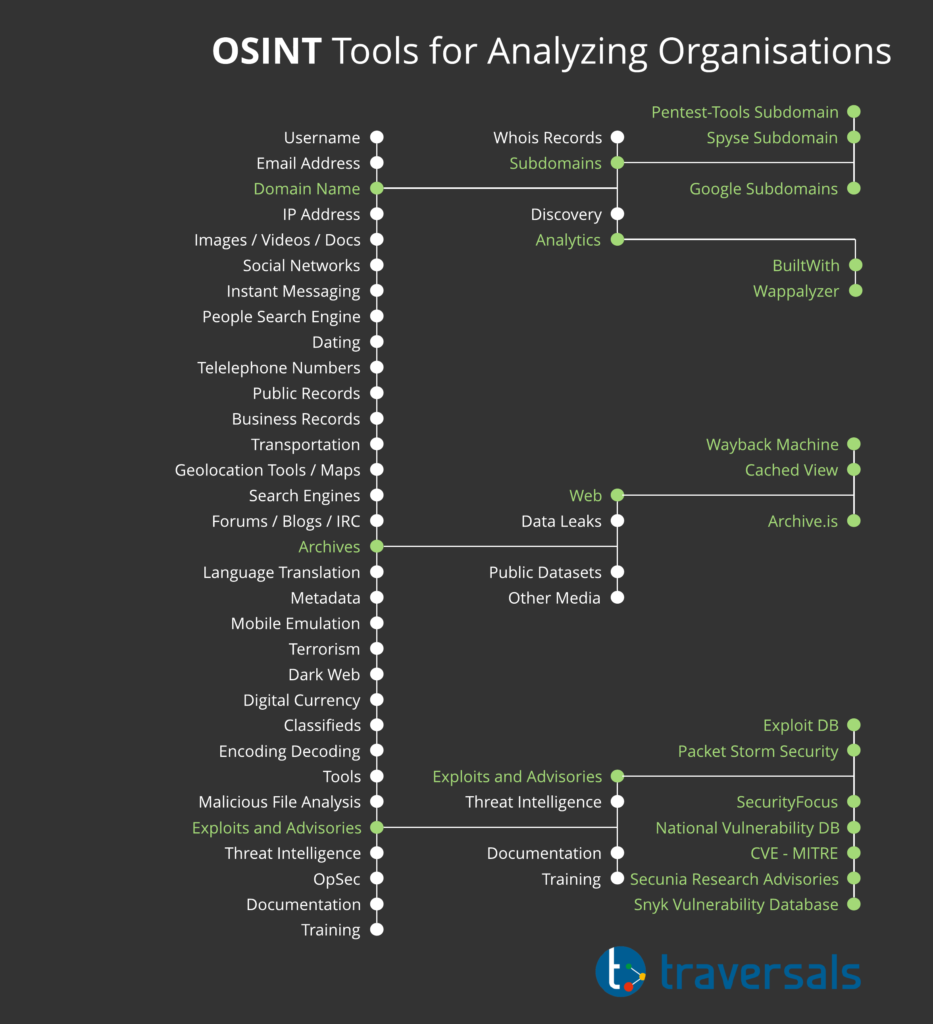
15 Powerful OSINT Tools for Analyzing Organizations
Open-source intelligence (OSINT) refers to the collection and analysis of publicly available information, mostly from online sources. The huge amount of digital data is considered the biggest challenge of any OSINT collection activity. Fortunately, there is a plethora of OSINT tools and techniques that can be used to assist the OSINT assemblies in this task.
OSINT requires much more than just using Google.
In today’s information age, OSINT can be used in various areas as written in our first OSINT white paper. Companies use it to monitor their competitors, to gain insights into market trends and customer perceptions of a certain product/service.
Governments and law enforcement agencies, on the other hand, use it to fight crime and terrorism, to predict global trends, and to provide timely and actionable information to policymakers in order to make informed decisions.
In the cybersecurity domain, OSINT tools are used to discover leaked data or to capture vulnerabilities in IT systems in addition to its important usage in counter-intelligence activities (identify and counter threats to IT systems originating from cyberspace).
At Traversals, our analysts and advisors are constantly looking for new OSINT features to integrate into our Data Fusion Platform. We use OSINT for the detection of data leakage, the risk assessment of your vendors, or for the analysis of your competitors.
In this white paper, we want to share powerful OSINT tools, online services, or tactics with you. These tools are your entry point to gather intelligence from the internet about any organization or entity. If you need more tools, please have a look at the OSINT Framework.
Digital Footprint of an Organization
Technical footprinting, also known as cyber reconnaissance, is the first task conducted by penetration testers and attackers before launching an attack. Your goal as a hacker is to gather as much information as possible about your target’s IT system, such as
- exposed ports,
- running network services,
- DNS names and IP addresses,
- remote access capabilities,
- unpatched vulnerabilities in applications and operating systems,
- or the type of security mechanisms in place.
The footprint analysis reveals potential entry points and the size of the target network. In a broad sense, footprinting is considered a part of OSINT.
However, OSINT does not stop at collecting technical information. You can apply OSINT analysis to any entity including individuals by examining all available public sources such as Facebook, Twitter, LinkedIn, Instagram or other services.
Now, to understand how you can use OSINT tools practically to collect a wide range of information about any entity online, let’s say we have a website of an organization where information must be collected legally.
Discover the Technical Footprint of an Organization
The first technical information we need to gather about any website is the type of web technologies used by it, such as
- analytics and tracking services,
- advertising system,
- web and email hosting provider,
- content management system,
- widgets of the website,
- programming language,
- JavaScript libraries and functions,
- operating systems and
- webserver types.
By knowing this information, we can research for vulnerabilities that target any specific technology. There are many online services for gaining information about a website’s technology. The two most popular are:
The given figure shows how we used the BuiltWith service to retrieve information about the organization in question. The results returned were comprehensive and open the door for further investigation into every technology used on this site.
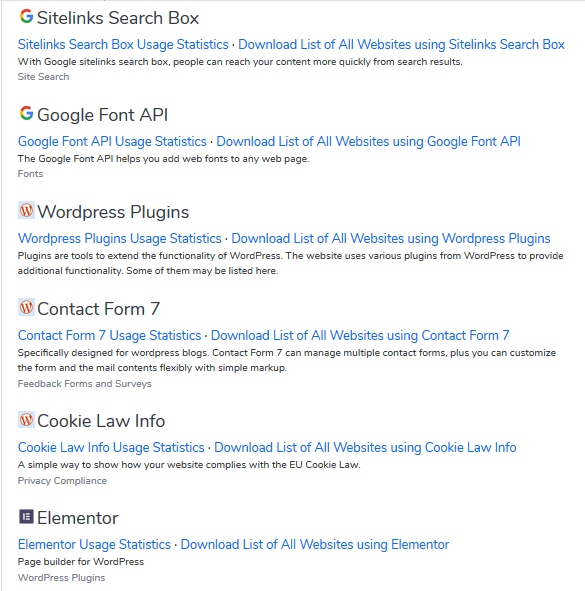
Armed with this information, we can go to vulnerability databases that list security vulnerabilities and exploits associated with each technology and operating system.
For instance, in our previous example, the target was using WordPress as a content management system. Thus, we go to CVE Details and search for vulnerabilities associated with WordPress.
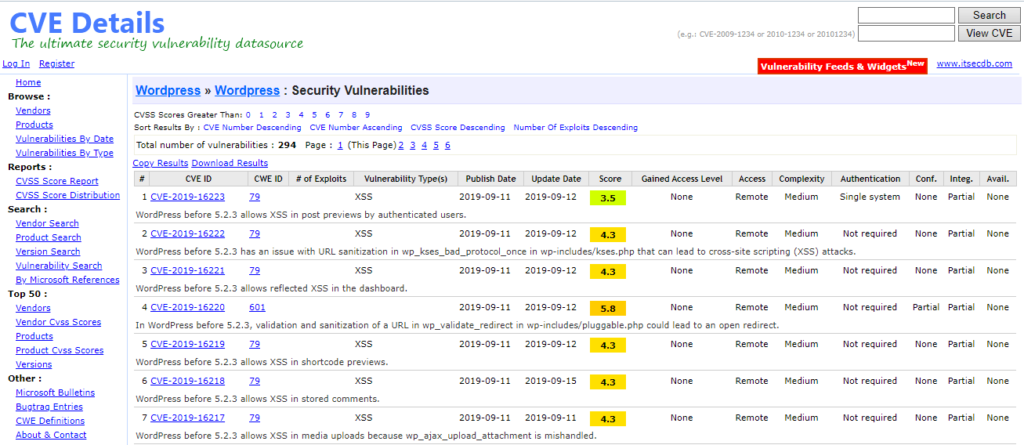
There are many online repositories with databases of vulnerabilities and exploits. The following are the most popular:
- Exploit Database – Exploits for Penetration Testers, Researchers, and Ethical Hackers
- Packet Storm Security
- SecurityFocus
- National Vulnerability Database
- CVE – Common Vulnerabilities and Exposures (CVE)
- Secunia Research Advisories
- Snyk Vulnerability Database
You may ask yourself now, why you should do an analysis like this. Analyzing the vulnerabilities with OSINT tools is of high interest when it comes to vendor risk management or technical due diligence.
According to Gartner, cybersecurity ratings will become as important as credit ratings when assessing the risk of business relationships.
Are you interest in cooperating with an organization or even acquire an organization that lacks cybersecurity?
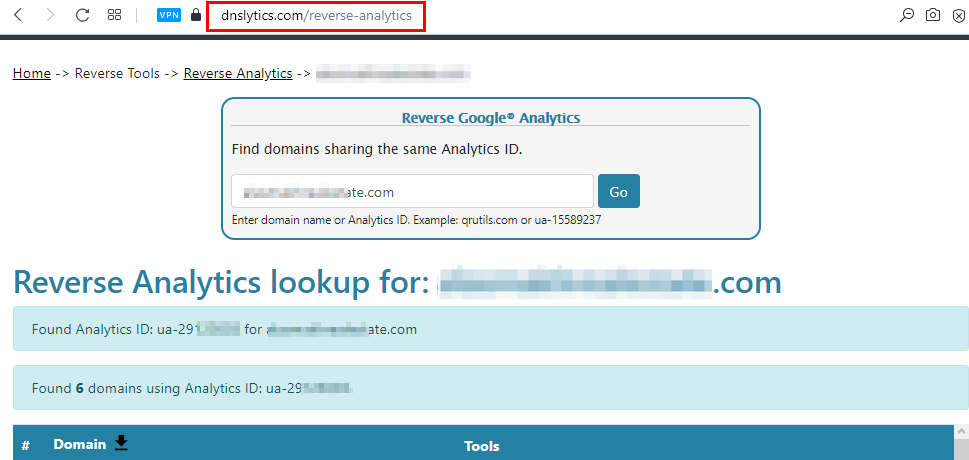
Identify Linked Websites
Sometimes, a business may have more than one website. OSINT tools can help us to discover multiple websites owned by a particular company. Such information has great intelligence value for competitor intelligence.
Are there more services run by the organization?
There are many technical methods to find linked domain names. However, it may not work if a company owns another domain name that is in no way linked to its main domain name.
Google Analytics, which is a service for measuring your advertising ROI, can be utilized to get this info by following these steps:
- Go to Reverse Analytics ID and enter the target domain name or its Google Analytics ID in the Reverse Google Analytics search form.
- If the target website uses Google analytics and there is more than one website using the same Analytics ID, a list of websites sharing the same Analytics ID will appear.
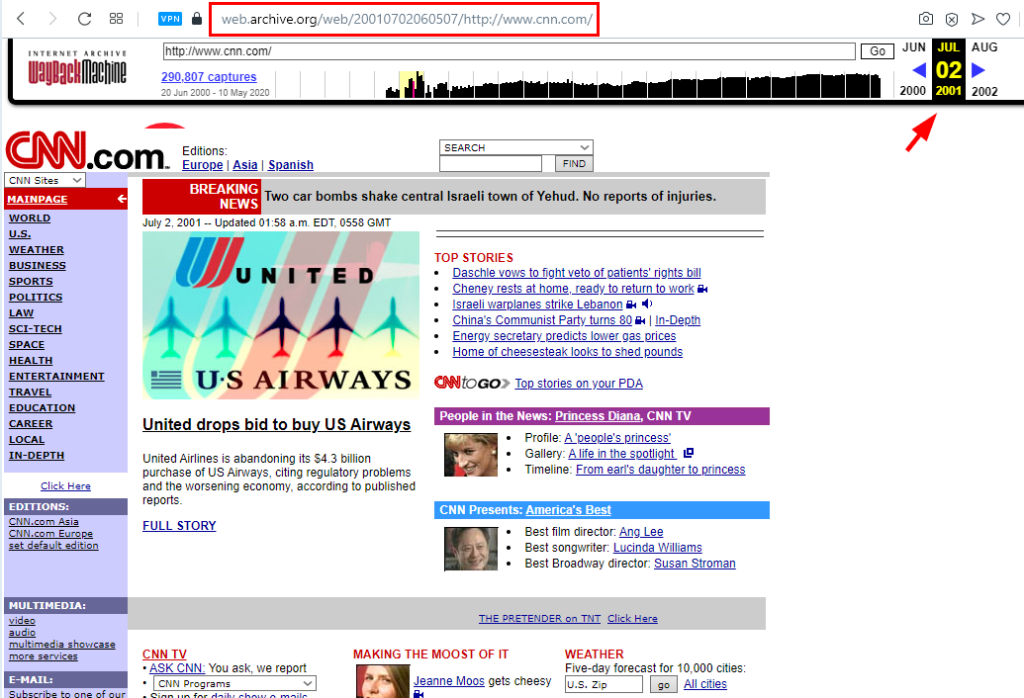
Analyze Historical Information
The digital archive of the World Wide Web reveals important information about the history of any website. The collected information may contain
- former product information,
- phone numbers,
- email addresses or
- metadata info of photos and videos pulled from the archival version of the target website.
The most popular archive site is the Wayback Machine.
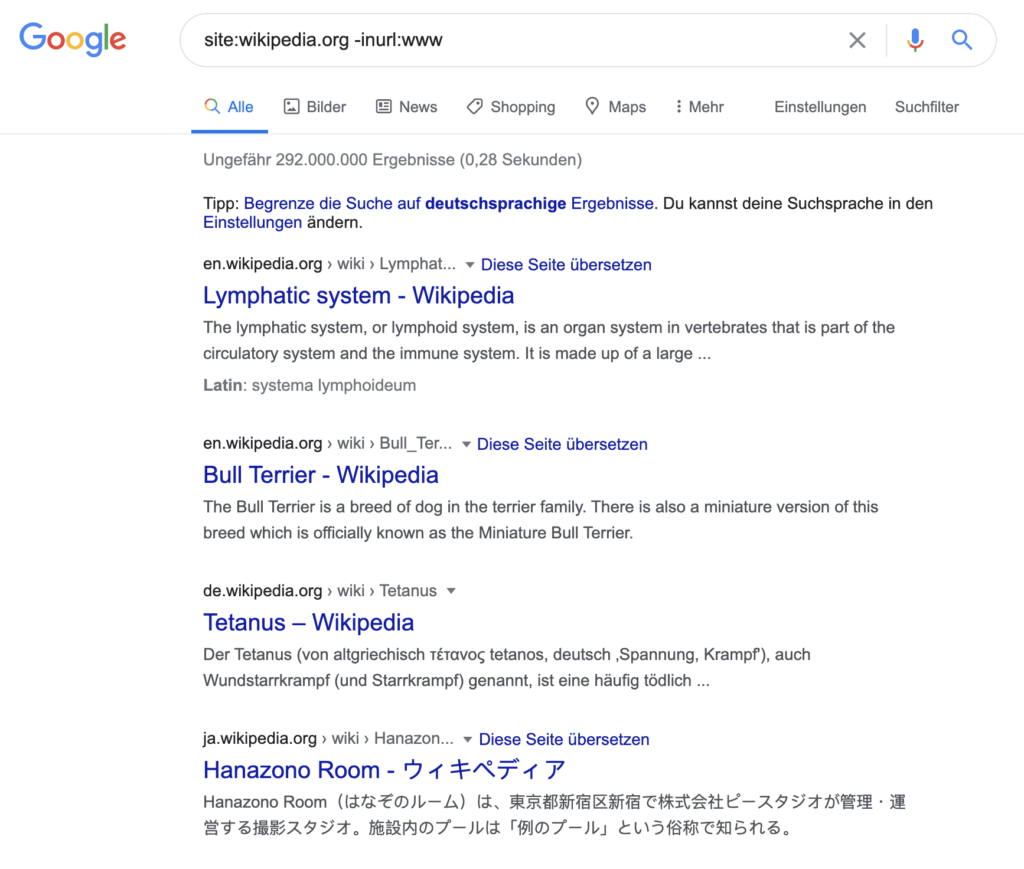
Discover Subdomain Names of an Organization
Subdomain name discovery is an essential part of the reconnaissance phase and also useful for competitor intelligence.
Are you interested in all subdomains linked to customers of specific SaaS companies?
For vendor risk assessment, we can expect to get a great deal of information by revealing all subdomains of the target domain such as:
- Forgotten subdomains that might host important files that left unprotected.
- Subdomain names that reveal important services running by target organizations, such as VPN, FTP, Webmail, …
- Subdomain names that are used to test web applications before deploying it in a production environment.
There are many online OSINT tools for subdomain discovery:
We can also use Google for subdomain discovery by utilizing the “site” operator.
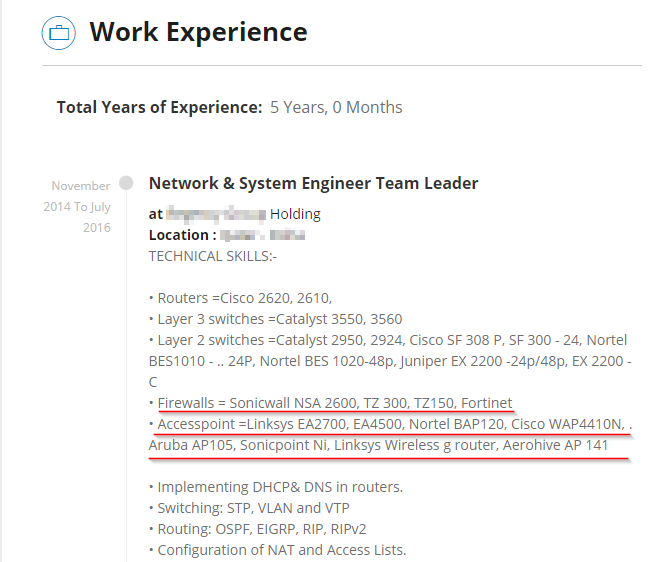
Identify IT Systems and Devices of an Organization
Using traditional tools, it is difficult to identify IT solutions of organizations. OSINT tools can help to identify the IT infrastructure.
Career websites hold millions of resumes of job seekers available publicly for anyone who wants to view them. A simple search on one of these sites can reveal important information about the critical security systems and types of servers and networking devices used by the target organization.
Finding Sensitive Information Using Google Advanced Search Operators
Advanced Google search operators, also known as Google dorks, can be used to find sensitive files online.
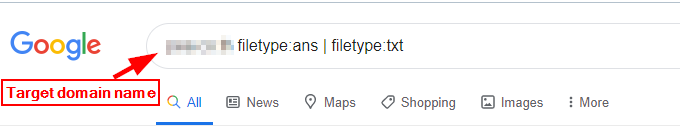
For example, we have tried to find all text files hosted on a target domain name. We were lucky enough to find an important file that contains password hashes of some of the target accounts.
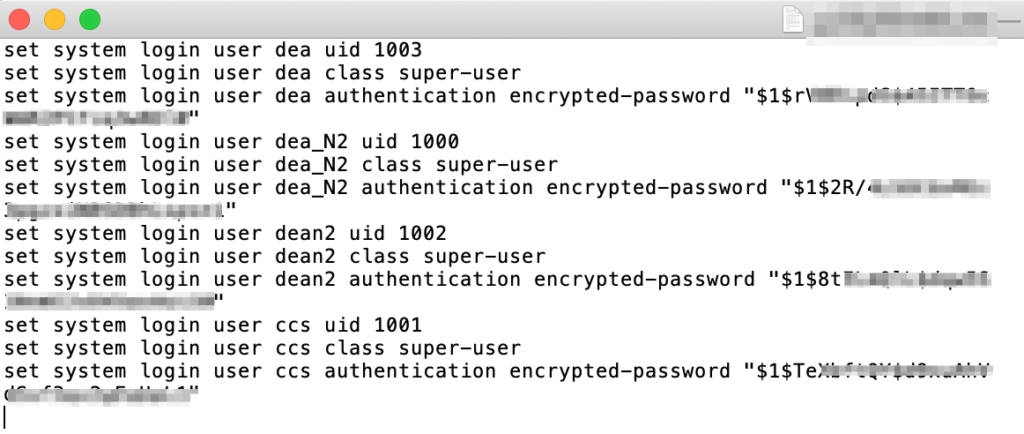
In the same way, we can search for leaked account credentials on Pastebin or anonymous file sharing websites using advanced Google dorks.
Closing Summary
Whatever your goals are, OSINT techniques can be used to collect information about any entity online. In this white paper, we have tried to give a practical example that shows how OSINT tools can be used to track the digital footprint of an organization. But as you can see, such an analysis is time-consuming and requires expert knowledge.
At Traversals, we spend a huge effort to automate more and more OSINT analysis steps and to make them available for our solutions based on the Data Fusion Platform.
Copyright © 2026, Traversals Analytics and Intelligence GmbH. All Rights Reserved.