
- Offers
- Product Philosophy
- Products
-
-
-
Traversals Government
- Ukraine Dynamic Frontline MonitoringAllows organizations to track frontline changes in almost real-time.
- Emerging Diseases RadarAllows organizations to identify new and emerging diseases in near real-time.
- Multi-Source Data Fusion PlatformAllows organizations to set up enterprise multi-source data and information fusion.
- Custom ServicesCustomized services can be provided at any time.
-
-
-
- Technology
- Company
-
-
-
Who We Are
- Our StoryMake Data Speak Your Language – Data fusion for comprehensive transparency, security and a secure basis for decision-making.
- CareersAre you interested in contributing to the development of exceptional solutions?
- ContactGet in contact with us if you need customized services or have questions.
-
-
-
Legal Information
- Legal Disclosure
- Privacy Policy
-
-
-
- Blog
- Contact Us
- Login
Data Leakage Best Practices for Your Organization
Key Takeaways
- No matter how hard we try, we cannot protect 100% of our company data with Data Loss Prevention.
- To deal with data leaks appropriately, a suitable interaction between prevention and detection is necessary.
- Our OSINT-based Data Leakage Detection lowers the cost of prevention, detection, and damage control, resulting in a rapid ROI.
What you should know from day one is that data leaks can cause serious damage to your business, regardless of the size of your organization. Even if you are not a cybersecurity expert, you should have a good understanding of the data leakage practices. Have you ever asked your IT staff:
How long does it take to become aware of leaked data and what is our plan if all our financial information, employee credentials, or customer data becomes publicly available?
As a manager, you are responsible for the protection of your assets, customers’ loyalty, revenue, or stocks. Hence, detecting data leakage is a must for every serious company.
You can invest a lot of money in data protection solutions. Unfortunately they do not provide 100% protection. For this reason, you should also deal with the discovery of leaked data.
In this white paper, we give you some insights into the data leakage best practices. We explain which forms of data leakage occur most frequently, how to prevent them, and how to detect them quickly and efficiently.
What is Data Leakage and Why do You Need a Detection?
Data leakage is an uncontrolled or unauthorized transfer of classified information to the outside world. You can call it a nightmare for your company, as the loss of information is associated with high fines according to GDPR, damage to reputation, and loss of business.
For most of companies, it takes 197 days to identify a data leakage, according to the 2018 Cost of a Data Breach Study by the Ponemon Institute. Let’s get clear, if you can identify and combat an incident within 30 days, you have a significant advantage over your less responsive competitors and save an average of $1 million in containment costs.
Penalties and damage to reputation are only a small part of your problem. Threat actors, like APT-28, leverage exposed data as part of the OSINT reconnaissance stage of their campaigns, as explained in our OSINT article. Threat actors use this information to exploit your organization and launch more targeted cyber attacks resulting in even higher damages.
Data leaks cause a high loss of money. You should try to prevent and detect this.
Some Practices for Data Leakage Prevention
A study conducted by Symantec says that more than 40% of data breaches are caused by insiders’ or employees’ negligence. Data is lost either accidentally or on purpose.
- You can deploy so-called Data Loss Prevention solutions in your stationary IT infrastructure. Some of them require client software running on each machine which continuously scans for restricted content. Other solutions are integrated into mailing systems analyzing all information that leaves your protected area. Both solutions result in high personnel and license costs. Our survey has shown that only large corporations afford this luxury.
- In our article Moving Target Defense, we described how to replace the stationary IT infrastructure with a dynamic approach. This concept creates a changing attack surface which makes it hard for threat actors.
In sum, there are a lot of different ways to prevent data leakage. There is a simple problem with it: Data leakage prevention solutions are not sufficient and we will explain why.
Use OSINT Methods for Identifying Data Leakage
In recent years, we have met many companies that have invested a great deal of effort and budget in securing their IT infrastructure to prevent data leakage. The shot backfired.
Sales managers and developers were no longer able to work with IT in a meaningful way and switched to using their private and non-secured IT. This can be proven very easily by having a closer look at the Dropbox hack 2012. Our insights confirm that costly data loss prevention solutions were circumvented.
We collected and analyzed a lot of data services on the surface, the deep and dark web, and explain a shortlist of them in this section.
- A simple solution is the service HaveIBeenPwnd. It gives you the possibility to check your own email address for breaches. The service is updated regularly and is a good starting point for detecting data leakage. However, you have to bring a lot of time with you, because a lot needs to be done manually. The service mainly reports data leaks with a high impact and is no help for targeted actions against your company.
- You should ask your software developers if they know Pastebin. You will be surprised by what Pastebin has already been used for by your developers. Pastebin is one of the data-sharing platforms which allows an anonymous posting feature and is often used for cooperation with external freelancers and also hostile hackers. You need Pastebin & Co on your watch list. Services like PasteMonitor can be used to automatically track certain keywords. Keep in mind that pastes only have a short lifetime and are deleted by the poster when the purpose of the paste is fulfilled. This means that you have to be fast to identify a leak.
- Another challenge is posed by lost documents. There are no special services for this, so you have to be proactive yourself. You can run special searches using Google Dorks, as shown in the screenshot. The given example is rather simple. Usually, Google Dorks searches with a focus on leaked documents are more complex.
Why do You Need Traversals’ Data Leakage Detection
We presented a shortlist of effective tools and services to identify data leakage. You have to ask yourself whether you have enough knowledge and personnel to implement the mentioned data leakage best practices.
Our Federated Search provides one powerful interface to the above-mentioned services. It is not necessary to call the services separately which would be very inefficient, as explained in our blog post. In our Data Leakage Detection, we spent a lot of effort on automating most of the procedures.
It can be said that Traversals’ Data Leakage Detection is self-learning in order to provide analysts with the best possible support. All data leakage searches are performed autonomously by the system. In a dashboard, you see which leaks exist and how the leak is assessed in terms of criticality.
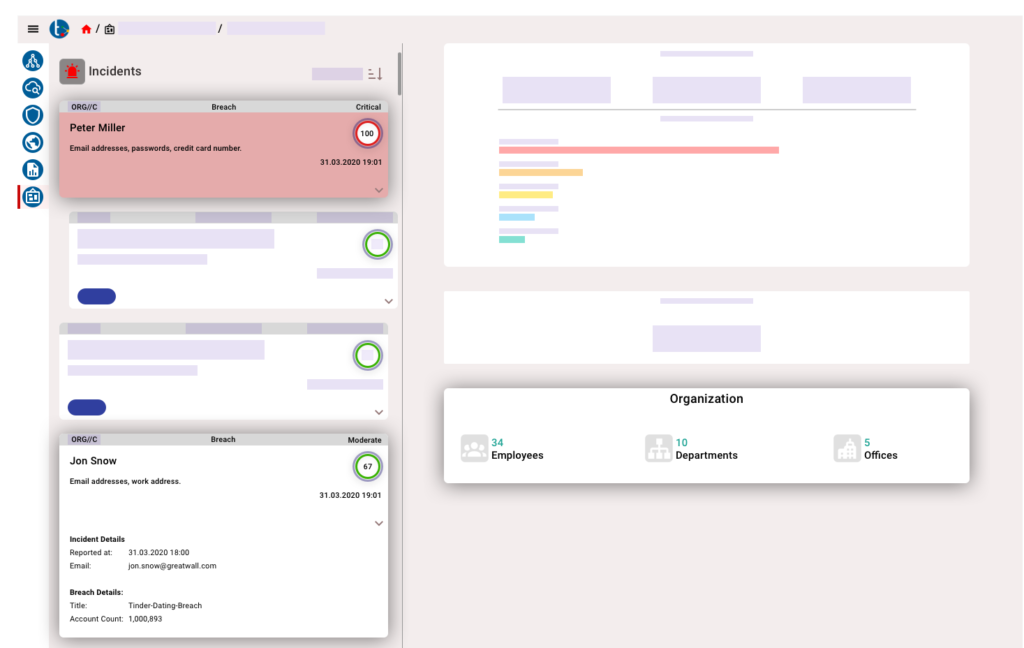
In order not to lose the overview, a task is created in our Investigation Platform for each incident. You can use the investigation platform for further analysis and find out:
- If the data leakage is coincident.
- If there is a specific reason and cause behind it.
- If it can be linked to a specific person.
- If there is a new trend.
Our Data Leakage Detection organizes the incident collection and handling resulting in a rapid ROI.
Key Takeaways
As you can see, data leakage detection is a crucial element, and more than important for companies of any size:
- No matter how hard we try, we cannot protect 100% of our company data with Data Loss Prevention.
- To deal with data leaks appropriately, a suitable interaction between prevention and detection is necessary.
- Our OSINT-based Data Leakage Detection lowers the cost of prevention, detection, and damage control, resulting in a rapid ROI.
Copyright © 2026, Traversals Analytics and Intelligence GmbH. All Rights Reserved.
